Vishing and smishing: The rise of social engineering fraud
- Published
Hackers use social engineering - essentially tricking people into breaking normal security procedures
Most of us like to think we're too clever to be caught out by email and telephone scams, but in fact any of us can get caught out by fraudsters.
Their tricks have gone far beyond the infamous fax from a "Nigerian prince" you've never heard of asking you for money.
Now frauds are increasingly sophisticated and you are much more likely to hear from someone you trust.
Fraudsters dupe their victims using a type of psychological manipulation known as "social engineering".
It is essentially a confidence trick that influences a person to take action that may not be in their best interest.
With many technical security defences in place to prevent banks and companies from being hacked directly, it is we humans that represent the weak spot that criminals seek to target.
To explain how they do this, security expert and self-professed 'Human Hacker' Chris Hadnagy uses the psychology behind the parent-child relationship.
"Children are little people that get us to do things we'd never thought we would ever do," he says, and the same psychological principles can be applied to the scammer.
Social engineering fraud losses doubled in 2015
They build rapport, get us to like them, trust them, and often inject a sense of urgency into the scenario, he says: "This all releases certain chemicals in our brain that allow us to take an action we perhaps shouldn't take."
Why is it growing?
Social engineering fraud has been identified by the international police agency Interpol, external as one of the world's emerging fraud trends.
In the last two years there has been a spike in this type of fraud, with reported losses in 2015 doubling to nearly $1bn (£675m) - though, by comparison, global credit card fraud was $16bn last year.
It's a lucrative crime.
You don't need a skilled programmer to do social engineering - just someone who's willing to talk to people or write emails.
On top of this, the growth of the internet has played right into the criminals' hands. A key part of social engineering is having information on your target.

Fraudsters aim to build rapport, to get us to like them and trust them, says Chris Hadnagy
Criminals can get this from buying hacked company data and studying their victim's social media profile online.
Vishing
In June last year Emma Watson, a British businesswoman who was setting up a children's nursery, got a phone call from her bank's fraud team.
They told her that they had stopped some unusual transactions on her account, but because it had been compromised she had to transfer her money into some other accounts they had set up in her name.
"They were completely professional, it was a clear line, they knew my name, they called me on my landline, they used all the language," she says.
"They were very reassuring, saying 'I know this is a distressing time for you and I'm going to help you'."

Emma Watson lost £100,000 to fraudsters
In fact it wasn't her bank calling at all, but criminals fraudulently posing as her bank's fraud team.
Emma ended up transferring £100,000 into the fraudsters' accounts online. Only a fraction of it has so far been traced and returned.
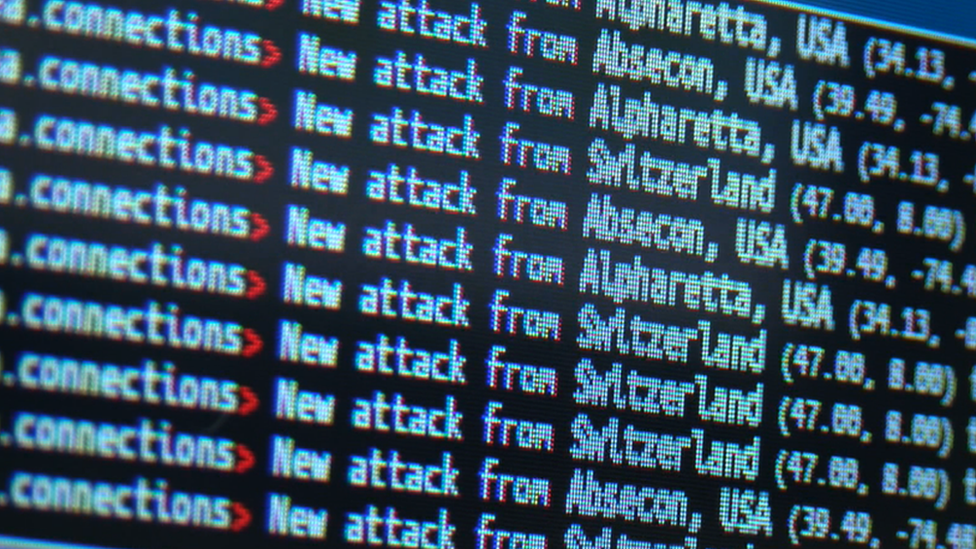
This type of fraud is called "vishing" where criminals persuade victims to hand over personal details or transfer money, over the telephone. They have a number of techniques at their disposal.
Information: the criminals already have your name, address, phone number, bank details - essentially the kind of information you would expect a genuine caller to have
Urgency: You are made to believe your money is in danger and have to act quickly - fear often leads people into acting without thinking
Phone spoofing: The phone number appears as if it's coming from somewhere else, so when you pick up the phone you already believe the caller because the number is convincing
Holding the line: In some cases, the criminals can hold your telephone line, so if you hang up to call back the bank, you can get put straight back to the fraudsters.
Atmosphere: You hear a lot of background noise so it sounds like a call centre rather than a guy in a basement - they either do have a call centre, or are playing a sound effects CD
Chris Hadnagy has this advice.
"Don't ever give personal information like banking or credit cards over the phone to someone who has called you.
"If you get a call, hang up, and ring the number on the back of your credit card using a different phone from the one they called you on."
Phishing
Phishing emails have risen in number and have got a lot more sophisticated.
Jessica Barker, an independent cyber security consultant, explains how they work.
"They play on your trust and they use a front, whether it's a bank, a friend's name, or someone you expect communications from, and they put urgency on you to try and worry victims into responding."

Phishing emails have risen in number and have become a lot more sophisticated
Chris Hadnagy says he was phished only recently, when preparing for a conference in Las Vegas.
"I had 30 things on order from Amazon being shipped out to this hotel in Vegas.
"The week I'm leaving the office is a wreck, I'm packing boxes, running back and forth, and I get this email that just says 'one of your recent orders will not be shipped due to a declined credit card'."
The email looked convincingly like one from Amazon. Chris clicked the link and it opened up what looked like a real Amazon log-in page.
He started logging on until he looked up and saw the address in his browser was from a Russian website.
"It wasn't Amazon.com, and I go 'woah, I just got phished'. The email was for two things I'd never ordered. It's a lesson I tell people, if you hit the right emotional triggers at the right time, anyone can be a victim of phishing."
Phishing emails can look very convincing, copying branding and 'spoofing' email addresses to make them look genuine. Jessica Barker offers this advice for spotting the scam.
Hover the mouse over the link and the URL details will come up and will show if it's valid, or taking you somewhere unrecognizable
If in doubt, don't click on the link
Open up a new web page in your browser, go to the website, log in that way and see if you have a notification there
If an email looks genuine then contact the sender through their official website
Never using telephone numbers or links provided in the email
Criminals will often study their victim's social media profile online
Smishing
"Smishing" is SMS phishing where text messages are sent trying to encourage people to pay money out or click on suspicious links.
Sometimes attackers try to get victims on the phone by sending a text message asking them to call a number, in order to persuade them further.
Unsolicited text messages from unknown numbers should raise alarm bells, but often banks do text their customers for a variety of reasons.
In that case, you should call the bank using a number from a bank statement or a verified source, not a text message.
For more on this, listen to World Business Report's How not to be the Victim of Internet Scams, on BBC World Service at 18:32 GMT on 1 Jan 2016, or click here
- Published17 November 2015
- Published15 October 2015

- Published6 March 2015
