Russian Fancy Bear hackers' UK link revealed
- Published

Russian hackers spent well over $6,000 at Crookservers
When Russia's most notorious hackers hired servers from a UK-registered company, they left a trove of clues behind, the BBC has discovered.
The hackers used the computers to attack the German parliament, hijack traffic meant for a Nigerian government website and target Apple devices.
The company, Crookservers, had claimed to be based in Oldham for a time.
It says it acted swiftly to eject the hacking team - dubbed Fancy Bear - as soon as it learned of the problem.
Technical and financial records from Crookservers seen by the BBC suggest Fancy Bear had access to significant funds and made use of online financial services, some of which were later closed in anti-money laundering operations.
Fancy Bear - also known as APT28, Sofacy, Iron Twilight and Pawn Storm - has been linked to Russian intelligence.

Some of Fancy Bear's activities had previously been identified by the cyber-security company Crowdstrike
The group played a key role in 2016's attack on the US's Democratic National Committee (DNC), according to security experts.
Indeed an internet protocol (IP) address that once belonged to a dedicated server hired via Crookservers was discovered in malicious code used in the breach
The spies who came in for milk
Early in 2012, Crookservers claimed to be based at the same address as a newsagent's on an unassuming terraced road in Oldham, according to historical website registration records.

More Coronation Street than Le Carre?
But after a short period, the listing switched to Pakistan. The BBC has seen no evidence the shop or its employees knew how the address was being used or that Crookservers had any real connection to the newsagent's.
Crookservers was what is known as a server reseller. It was an entirely online business. The computers it effectively sublet were owned by another company based in France and Canada.
The BBC identified Crookservers's operator as Usman Ashraf.
Social media and other online accounts suggest he was present in the Oldham area between 2010 and mid-2014. He now seems to be based in Pakistan.
Mr Ashraf declined to record an interview, but provided detailed answers to questions via email.
Despite his company's name, he denied knowing he had had hackers as customers.
"We never know how a client is using the server," he wrote.
When in 2015 he had been alerted to the hackers, he said, he had acted swiftly to close their accounts.
He said he had also carried out a "verification" process, culling 60-70% of the company's accounts he had suspected of being misused.
"There is 0% compromise on abusive usage," he said.
Joining the dots
Over three years, Fancy Bear rented computers through Crookservers, covering its tracks using bogus identities, virtual private networks and hard-to-trace payment systems.
Researchers at cyber-threat intelligence company Secureworks, who analysed information from Crookservers for the BBC, said it had helped them connect several Fancy Bear operations.

Mike McLellan of Secureworks said the hackers employed poor tradecraft
Senior security researcher Mike McLellan said the hackers had exhibited poor "tradecraft".
One communication shows one hacker, using the pseudonym Roman Brecesku, had complained that his server had been "cracked".
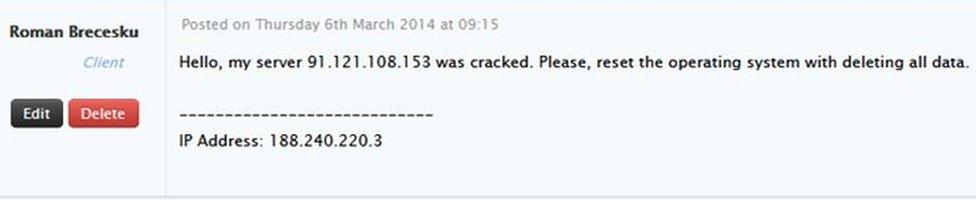
A Fancy Bear hacker, using a pseudonym, complained that his server had been hacked
Crookservers was previously linked to an attack on the German parliament, external.
The server used to control the malware was hired through Crookservers by a hacker using the pseudonym Nikolay Mladenov who paid using Bitcoin and Perfect Money, according to records seen by the BBC.
The hacker used the server until June 2015, when it was deleted at Crookservers's request following media reports of the attack.
This server's IP address also appears in malware used to target some attendees at the Farnborough air show in 2014, external.
Fancy Bear malware used to attack a UK TV station and the DNC also contained this IP address, although the server was no longer in Fancy Bear's control when these attacks occurred.
A financial account used by Mladenov was also used by another hacker, operating under the pseudonym Klaus Werner, to hire more computers through Crookservers.
One server hired by Werner received "redirected" traffic from a legitimate Nigerian government website, according to Secureworks analysis.
Apple attack
The financial account used by Mladenov and Werner was used by Fancy Bear hackers - including two using the names Bruno Labrousse and Roman Brecesku - to hire other servers from Crookservers.
One server and the email address used to hire it seem to have links to "advanced espionage" malware used to target iOS devices.
The malware was capable of turning on voice recording and stealing text messages, external.
Another email used to hire servers can be linked to an attack against Bulgaria's State Agency for National Security.
But there are eight dedicated servers tied to the same financial information, whose use is unknown - suggesting there may be other Fancy Bear attacks that have not been publicly disclosed.
Follow the money
Fancy Bear spent at least $6,000 (£4,534) with Crookservers via a variety of services that offered an extra level of anonymity.
They included Bitcoin, Liberty Reserve and Perfect Money. Liberty Reserve was later closed after an international money laundering investigation.

Tom Robinson of Elliptic tracked the source of some Fancy Bear payments
The BBC asked a UK company called Elliptic, which specialises in identifying Bitcoin-related "illicit activity", to analyse Fancy Bear's Bitcoin payments.
Lead investigator Tom Robinson said his team had identified the wallet that had been the source of these funds. He said the bitcoins it contained were "worth around $100,000".
Elliptic traced the source of some of the funds in that wallet to the digital currency exchange BTC-e.
In July, BTC-e was closed by the US authorities and its Russian alleged founder arrested in Greece accused of money laundering.
Although BTC-e is alleged to have been popular with Russian cyber-criminals, the BBC has no evidence its management was aware its clients included Fancy Bear.
Continuing operation
The financial and technical records link together several attacks previously tied to Fancy Bear.
And it is possible that following the financial trail further may yield additional revelations.
Crookservers closed on 10 October. Fancy Bear's operations, however, have not.
- Attribution
- Published6 July 2017

- Published25 April 2017

- Published20 September 2016
