Zain Qaiser: Student jailed for blackmailing porn users worldwide
- Published

Zain Qaiser scammed visitors to pornography sites around the world
A student who made hundreds of thousands of pounds blackmailing pornography website users with cyber attacks has been jailed.
Zain Qaiser from Barking, London, used his programming skills to scam visitors to pornography sites around the world.
Investigators have discovered about £700,000 of his profits - but his network may have made more than £4m.
Qaiser, 24, was jailed for more than six years at Kingston Crown Court.
The court heard he is the most prolific cyber criminal to be sentenced in the UK.
Judge Timothy Lamb QC said: "The harm caused by your offending was extensive - so extensive that there does not appear to be a reported case involving anything comparable."
His jail sentence of six years and five months is a second major success for the National Crime Agency (NCA) after the jailing earlier this year of a British man who broke an entire nation's internet.
Bedroom attack
Qaiser was first arrested almost five years ago - but the case has been delayed because of the complexity of the investigation and mental health concerns.
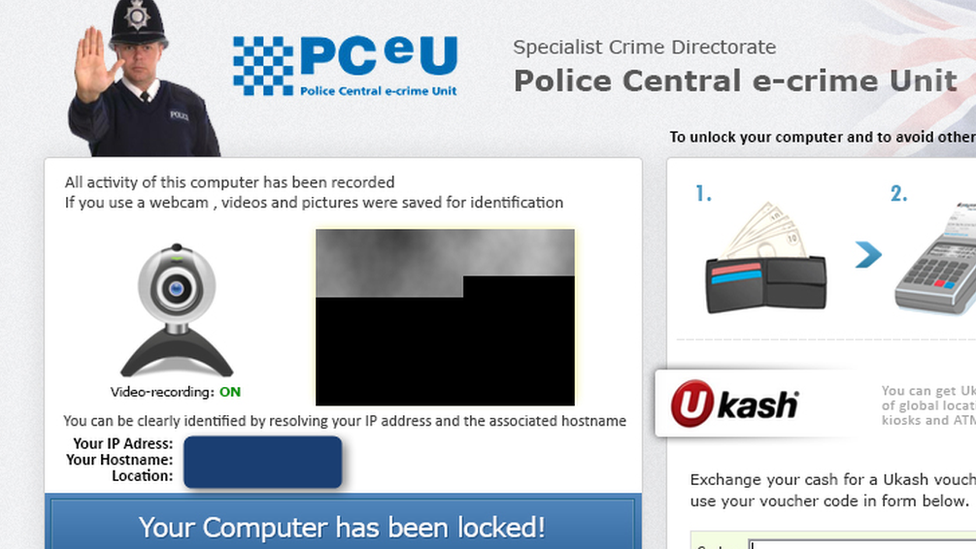
Scam: Qaiser tricked users into thinking they were going to be prosecuted
Initially working from his bedroom at his family home in Barking, Qaiser began to make money through "ransomware" attacks when he was only 17 years old.
This is a form of attack in which a computer is hijacked and frozen by a small piece of software until the user pays a fee for its release.
Millions of these attacks occur every day around the world - the most well-known example in the UK is the "Wannacry" attack on the NHS in 2017.
Qaiser contacted the Russian controller of one of the most potent attack tools and agreed a split of his profits if his planned blackmail operation was a success. In turn, he forged contacts with online criminals from China and the USA to help shift the cash.

Qaiser was filmed cashing in some of his money at a casino
Over 18 months, the teenager posed as a legitimate supplier of online promotions and booked advertising space on some of the world's most popular legal pornography websites.
But each of the adverts that was promoted on the websites contained a malicious tool called the "Angler".
Any visitor to the adult site who clicked on one of Qaiser's fake adverts would trigger the download to their own computer of the attack kit.
If the home computer was not protected with up-to-date anti-virus software, the Angler would search for vulnerabilities and, if possible, deliver the "ransomware" that seized control of the machine.
It immediately splashed a full screen message to the user, purportedly from the FBI and other law enforcement agencies, accusing the user of breaking the law - warning them they faced up to three years unless they paid an immediate fine equivalent to roughly $200 or £100.
"Out of fear of embarrassment from friends or family members discovering they had accessed pornography, many users paid the ransom," prosecutor Joel Smith told Kingston Crown Court.
"For obvious reasons very few people complained to law enforcement officials."
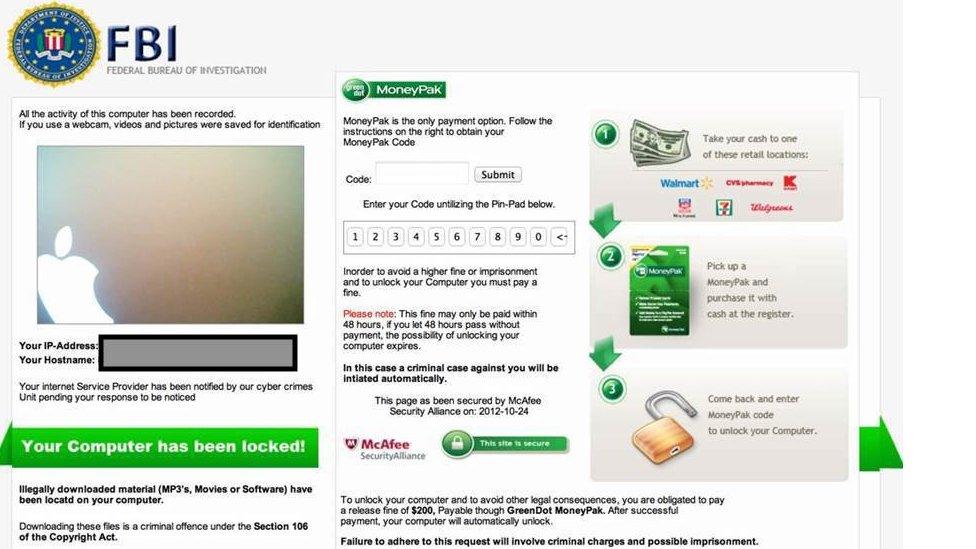
FBI scam: Victims saw a different bogus law enforcement page depending on their location
To make thing worse, the warning page claimed that police had captured webcam images of the user during their visit to the adult website - and gave a deadline for the payment to be made.
The National Crime Agency says that it's impossible to know exactly how many people paid up - but forensic data has revealed Qaiser's operation was enormous.
One screen grab from his control system reveals that he made £11,000 in July 2014 alone.

Qaiser's "control panel" showed his ransom demands hit 16,000 PCs in just one month
In a sampling exercise, the NCA calculated just one of the fake adverts appeared on 21 million web browsers every month - including 870,000 appearances on pornography pages accessed in the UK.
In turn, the attack kit would have been downloaded on approximately 165,000 PCs. Some 5% of those - about 8,000 users - were likely to have fallen victim to the ransom demand.
Financial investigators have established that Qaiser's operations shifted at least £4m through a string of crypto-currency platforms - although a great deal of these profits were ploughed back into the scam by buying more and more advertising space.
The NCA's financial investigators identified that the former computer sciences student had personally received almost £550,000 by the time of his arrest.
During the lengthy investigation while he was on bail, detectives found he received a further £100,000 as his associates moved funds through Gibraltar and Belize to a UK-accessible online account.
Qaiser is believed to have more stashed in online crypto-currencies because he revealed in online chats that he has further "offshore savings".

He was also filmed in an internet cafe
Mike Hulett, head of cyber investigations at the National Crime agency, said: "We regard Zain Qaiser as probably the most significant cyber crime offender that the NCA has investigated.
"The sheer volume and complexity of the actions - the number of people he is connected with worldwide and the frequency of his operation made it so successful and led to him making the money that he did.
"I don't think we will ever know the true number of people who paid up."
During his offending, Qaiser had no legal income - but he maintained a high-rolling lifestyle.
He spent almost £5,000 on a Rolex watch and £2,000 on a stay in a Chelsea hotel. He regularly spent money on prostitutes, drugs and gambling, including almost £70,000 in a casino in an upmarket shopping centre.
Threat to brokers
While it appears that no users of adult websites directly alerted police anywhere in the world, the advertising brokers who unwittingly placed Qaiser's malware promotions did.
When a Canadian company selling advertising space asked Qaiser to stop, he launched a massive cyber attack against it, causing hundreds of thousands of pounds worth of damage to the business.
"Really, it's just better if we work together," warned Qaiser in one message to the broker.
"We can make some serious money together. It's my way or no way. The K!NG is back."
The Canadian company contacted police.
Elizabeth Lambert, defending, said that Qaiser had suffered from bouts of mental illness and was influenced by older, more experienced organised cyber criminals.
Qaiser initially denied the crimes and claimed he had been hacked, before pleading guilty to 11 charges - including blackmail, fraud, computer offences and possessing criminal property.
The ransomware offences were committed between 2012 and 2014.
- Published11 January 2019